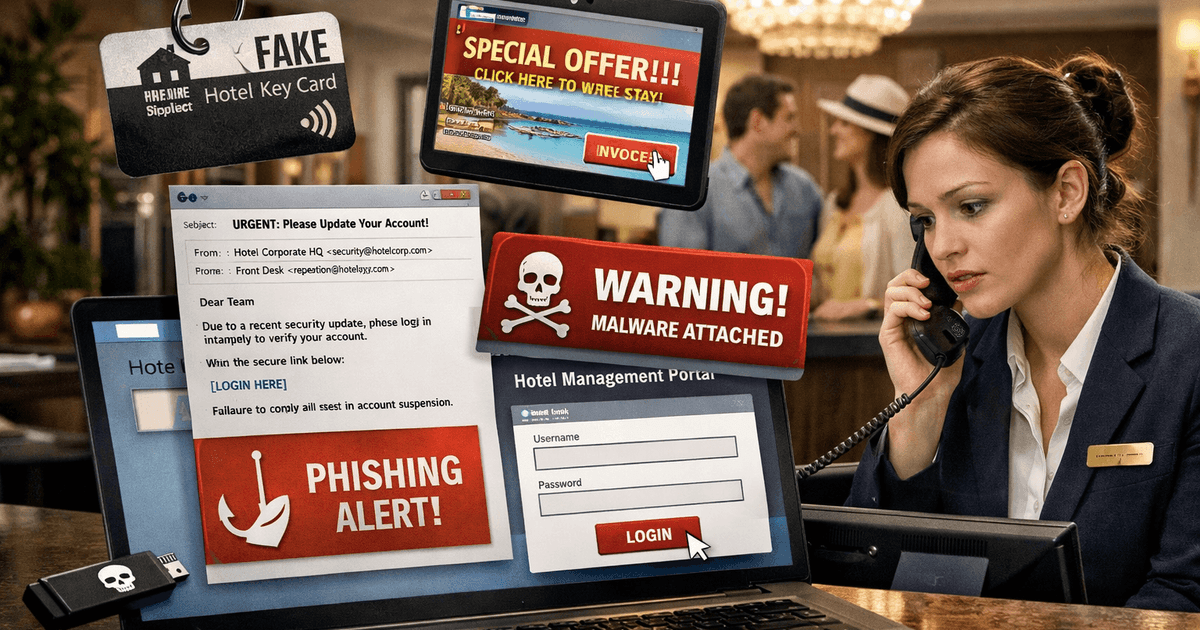
Hospitality businesses are being urged to strengthen their cybersecurity practices following a significant increase in phishing attacks within the industry.
Cybercriminals are actively targeting hotel property management systems and booking channels in an effort to harvest credentials, gain unauthorised access and ultimately exploit guest and business data.
In response to this, hostech giants, Guestline, part of Access Hospitality, Mews, HotelTime and Planet have shared an overview of the current industry landscape and how businesses can protect themselves.
The rise in phishing attacks in the hospitality industry.
Hostech giants, including Access Hospitality, Mews, Hotel Time and Planet, have all revealed their take on what they’re seeing happening in the industry currently.
Cybercriminals are actively targeting hotel property management systems (PMS), email systems, and booking channels. They are sending emails that appear to be from legitimate sources, including OTA platforms or internal systems, designed to trick staff into entering login information or downloading malware.
They start by tricking employees who manage hotel reservations into logging in to a fake system. They do this by creating nearly identical copies of system login pages and even buying similar domain names to lure unsuspecting users. Threat actors are using Google ads to get their sites to the top of the page.
Once they gain access via stolen credentials, attackers can send fake reservation confirmations or phishing emails to your guests, damaging trust and exposing sensitive guest information
Nicola Longfield, General Manager for Accommodation from Access Hospitality
Across the hospitality sector, phishing attacks are becoming far more targeted and contextual. Fraudsters are increasingly impersonating trusted brands such as hotels, booking platforms or technology providers, often mimicking real payment or booking scenarios.
The use of urgency, for example, failed payments or imminent cancellations
is a common tactic that pressures recipients into acting before verifying the request.Jan Hejny, CEO at Hotel Time
When asked about the current situation and how the industry is responding, Richard Johnson, Chief Information Security Officer at Planet, comments: “We work alongside hospitality teams to manage and reduce risk. Planet actively works with our security partners and with authorities to identify, disrupt and take down fraudulent activity, including websites impersonating legitimate businesses.
“Fraud is a full‑time operation for criminals looking for quick wins. By sharing intelligence quickly and raising collective awareness, we continually make it harder for them to succeed.”
The steps businesses can take to protect their business
Ian Trzoska, Security Analyst from Access Hospitality, comments, “These attacks can result in compromised hotel accounts, fraudulent communications sent to guests, and serious reputational or financial harm if not swiftly identified and mitigated.”
Access Hospitality has revealed the immediate actions hotel venues should take to protect hotel systems and data.
Upgrade to Phishing-Resistant MFA (Passkeys)
Ian commented: “We strongly recommend upgrading to passkey-based multi-factor authentication (MFA), which we consider the gold standard of security protection. Unlike traditional one-time password codes, passkeys provide phishing-resistant authentication that makes it virtually impossible for attackers to compromise your accounts, even with sophisticated phishing attempts. Even if you already have standard MFA, you are still vulnerable and need phishing-resistant passkey-based MFA.”
Passkeys offer superior protection:
-
They create a unique cryptographic link between your account and your official sign-in website. For example, for Guestline users, they will only work on the genuine Guestline login page and will not respond to fake or look-alike websites created by attackers – protecting you even if you accidentally click a phishing link.
-
As there’s no password or one-time code to type in, there’s nothing for staff to accidentally share in a phishing email, chat, or phone call. The secret part of the key never leaves your device, meaning attackers cannot copy it even if they see your screen.
-
Passkeys are both more secure than traditional MFA methods and typically faster to use. You simply confirm your identity by touching a physical security key (such as a YubiKey) or using your device’s biometric sensor, fingerprint, or PIN.
Flexible passkey options include physical security keys, such as YubiKey, Google Titan Security Key, or SoloKeys. You can also store passkeys on a mobile device or laptop, whether that is an Android or an iOS device.
Encourage staff to bookmark login pages and offer training
Be sure to bookmark official login pages rather than navigating via search engines, as this can expose you to look-alike phishing sites.
Also, employers should train all staff to identify suspicious emails. Encourage employees to watch out for unusual sender addresses, urgent language, unexpected attachments, or requests to share credentials.
Lastly, encourage an immediate reporting culture so that even uncertain suspicions are escalated and analysed without delay.
Use strong, unique passwords and avoid reusing them
We recommend using long, unique passwords and avoiding reusing them across multiple accounts or systems. Also, disable shared logins (like [email protected]) for critical services. Instead, assign individual accounts for staff with role-based access rights.
Keep software and systems up to date
Keep software and systems up to date with the latest updates and security patches; outdated software significantly increases vulnerability.
Also, deploy reputable antivirus, malware protection, and firewalls to detect and block malicious activity and finally, back up critical data regularly and test recovery procedures. Backups let you recover quickly if systems are compromised.